What is my IP? 🤔 💭
I like learning new stuff - anything, including technology. I love tinkering with new tools, systems and services, especially open source projects
A lot of times I access Togai infrastructure from my house using my house Internet. Togai's infrastructure is set up in such a way that any random IP cannot access the Togai internal infrastructure using SSH. Only certain IPs can SSH - say allow-listed IPs (the old racist term being whitelisted IPs).
We use AWS Cloud at Togai and have set up Network Security Group rules - both inbound and outbound rules, for all the EC2 servers we run. We use a bastion host to SSH into any machine in the Togai infrastructure and the bastion host is accessible only by some IPs defined in the Network Security Group rules - usually our office's public IP which never changes 😁 and then a few public IPs of people working from their homes
The public IP addresses of people working from their homes can often change because the Internet Service Providers (ISPs) could have a low lease period for a public IP, so it's not surprising to get a new public IP every day when switching on the router 🛜, and yeah, my router is not running 24/7 in order to save energy 🌱🪴⚡️.
Now, since the public IP keeps changing, we gotta keep adding our new Public IP to the Network Security Group Inbound rule so that we can access the bastion host and SSH into it and then SSH into all other machines accessible from the bastion host.
I created a small tool to help with allowing our public IP with ease instead of signing into the AWS console each time to find the correct security group and then modify it
The tool 🔨 🪚 is part of a set of tools I wanna call aws-tools - https://github.com/karuppiah7890/aws-tools
For now allow-ip is the only command supported in it. The syntax for the command is
aws-tools allow-ip <security-group-id> <rule-name> <ip-v4-address>
rule-name is nothing but the description of the rule so that it's clear to others about who or why the rule was created. This command does not overwrite any existing rule, which is something one may very much want to do - for example using rule-name / description as the unique identity of the rule to find the rule and modify it
There are other tools ⚒️ 🛠️ 🧰 out there that do pretty much the same thing and also do modification. I just wanted to create a small utility by myself and use it. It is such a breeze to create and use one's own tool 🔨 😁 But yeah, one has to be wary of that fact that it can take time 🕰️ - quite some time - depending on the tool, to build the tool, before using it
Anyways, so, I created the tool, and then stored the input for the tool in environment variables - mostly because they are all secrets or vary across different environments I work with - staging, sandbox and production, or both.
So, my .env files look like this -
export AWS_REGION=us-east-1
export AWS_ACCESS_KEY_ID=aws-access-key-id
export AWS_SECRET_ACCESS_KEY=aws-secret-access-key
export BASTION_SECURITY_GROUP_ID=security-group-id
I used to source the .env files, for example
source staging.env
And then run the below command to allow my IPv4 address
aws-tools allow-ip $BASTION_SECURITY_GROUP_ID karuppiah 49.37.211.173
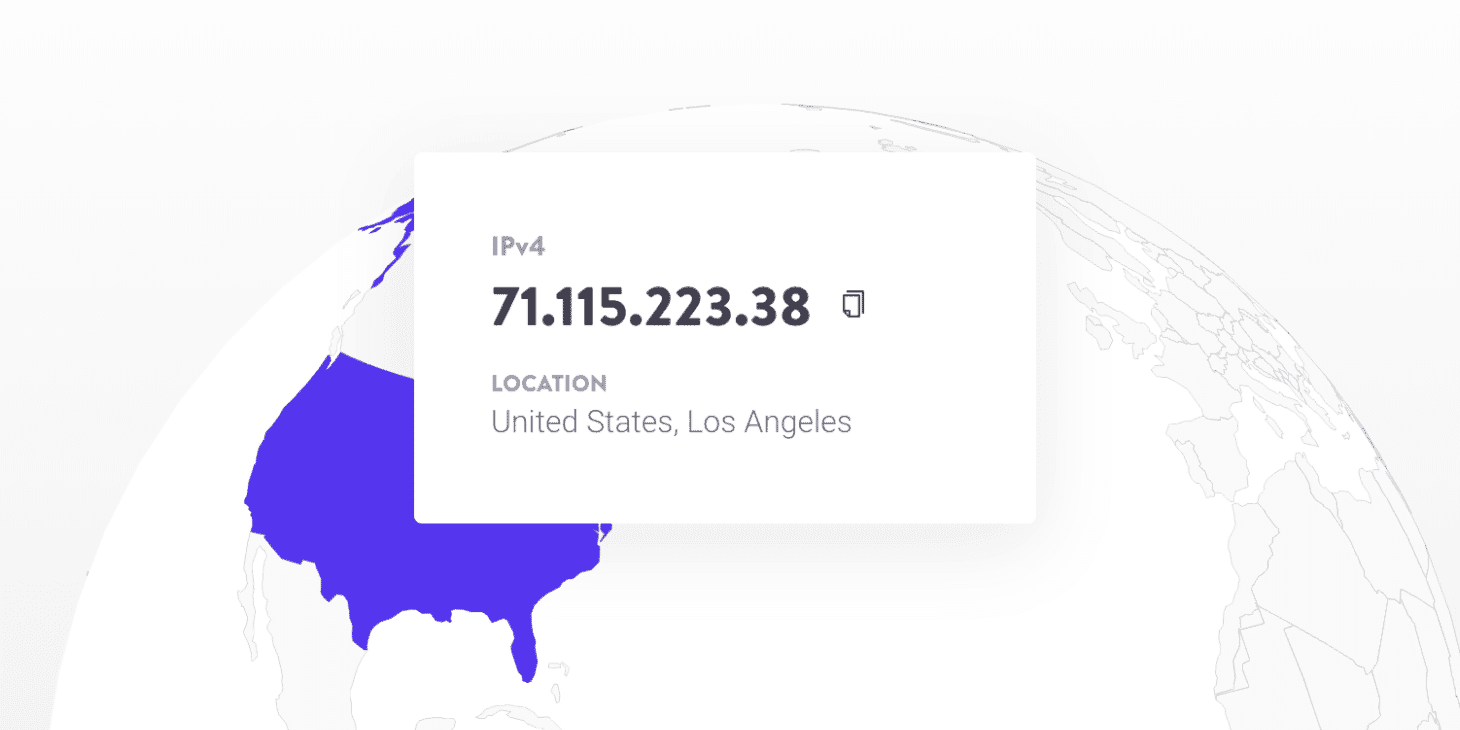
For this, I had to find my public IP address. There are many ways to do this. One way is - use your search engine - almost all search engines have the feature to tell your public IP, or any public service can tell your public IP - based on simple networking concepts. So, I use DuckDuckGo 🦆 or Google and both of them show public IPv4 IP addresses. Another way is to use other specific services online, for example https://ifconfig.me is one such service. I used to be able to curl https://ifconfig.me to get my public IPv4 IP address. But now, curl https://ifconfig.me gives me my public IPv6 IP address. So, now I use another method that my friend suggested -
dig @resolver4.opendns.com myip.opendns.com +short -4
So, now, I put it all in one ☝️ command -
aws-tools allow-ip $BASTION_SECURITY_GROUP_ID karuppiah \
$(dig @resolver4.opendns.com myip.opendns.com +short -4)




