Managing GitHub Organization Level Secrets for Private GitHub Repositories for Free on GitHub Free Plan using Terraform!
I like learning new stuff - anything, including technology. I love tinkering with new tools, systems and services, especially open source projects
We at Togai currently are on GitHub's Free plan, since we are still small and can't afford to pay for GitHub Team, let alone GitHub Enterprise, where the prices are seat-based (per user pricing)
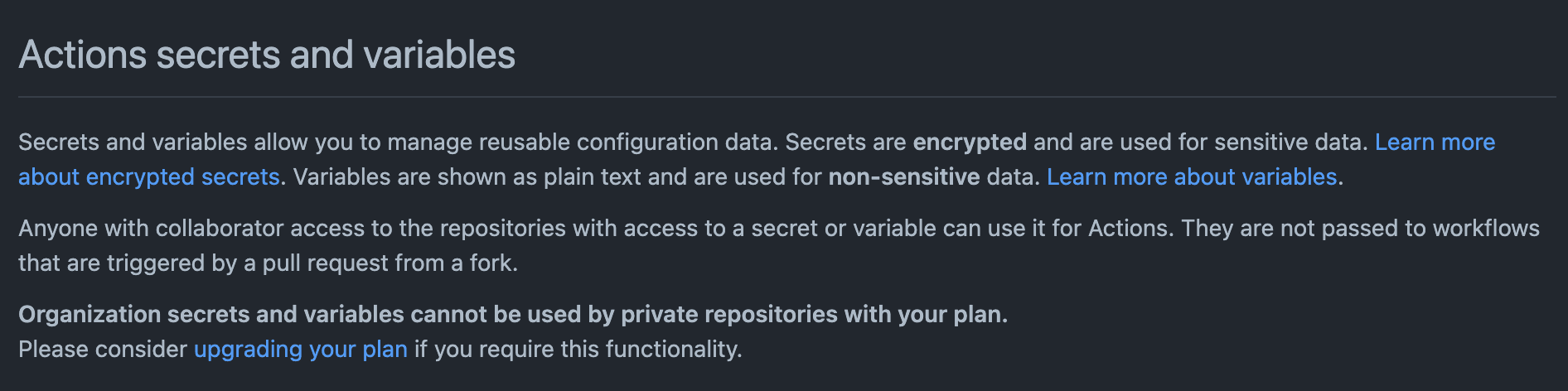
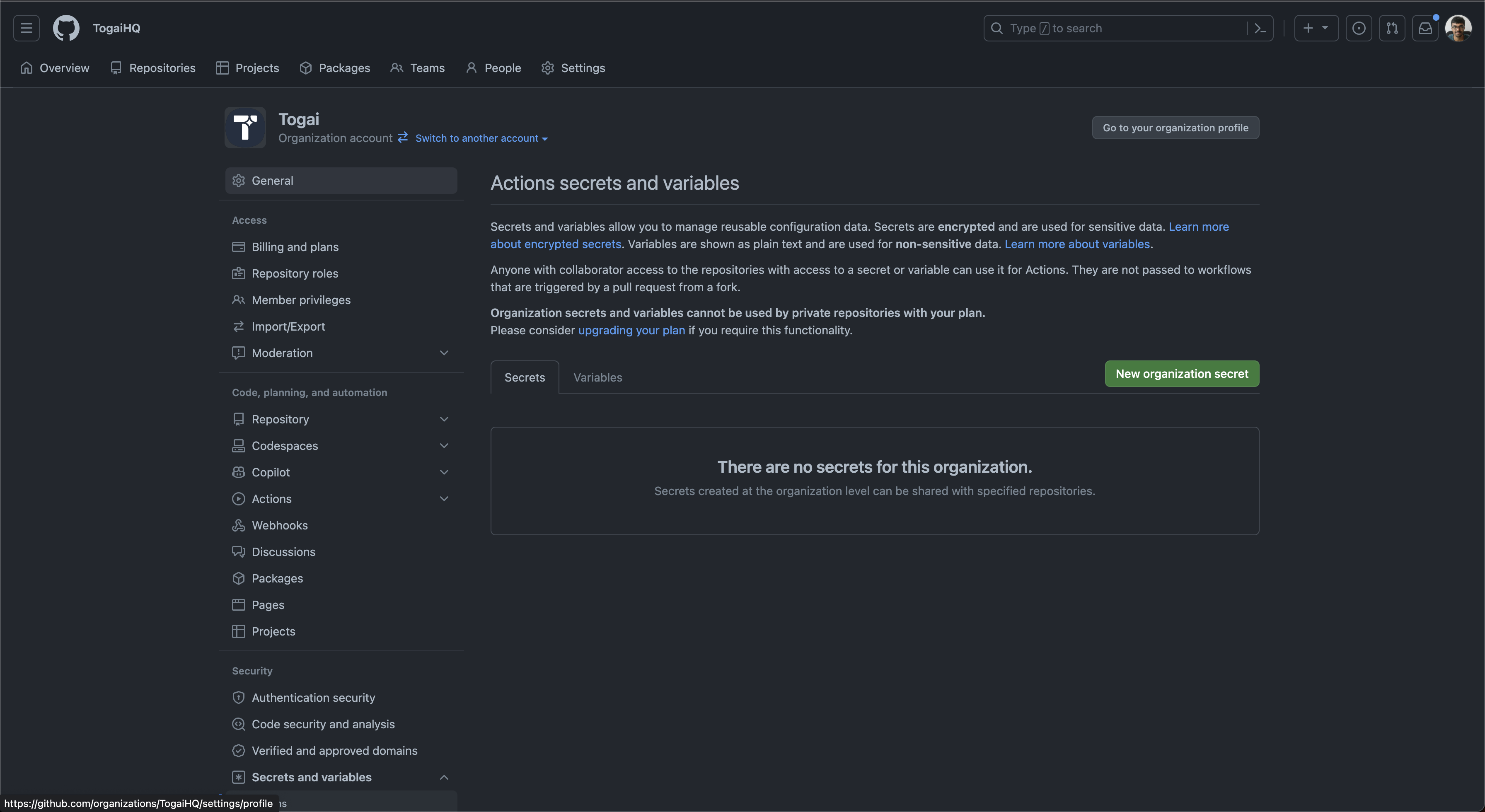
Of course, GitHub has some restrictions or lack of features on the GitHub Free Plan. One of the restrictions is -
Organization secrets and variables cannot be used by private repositories with your plan.
Please consider upgrading your plan if you require this functionality.
Screenshots attached below
But we needed a lot of GitHub Actions secrets to be common across many repositories (not all though) under the Togai GitHub Organization. These were some secrets used for the GitHub Actions CI/CD - as we are self-hosting GitHub Actions Runners on AWS which requires AWS secrets among other secrets for our implementation of Self-Hosted GitHub Actions Runners
In our case, these were the names of secrets we needed across many repositories and their values were the same in each repository
RUNNER_MANAGER_AWS_ACCESS_KEY_IDRUNNER_MANAGER_AWS_SECRET_ACCESS_KEYRUNNER_MANAGER_AWS_REGIONRUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKENRUNNER_MANAGER_SECURITY_GROUP_IDRUNNER_MANAGER_SUBNET_ID
In an ideal situation, I think we would have used GitHub Organization-level secrets and accessed them from the many repositories that require these secrets. But all the repositories that required these secrets were private and as GitHub had mentioned, private repositories cannot use GitHub Organization-level secrets
Now, what to do was the question I had in my mind. Of course, I wasn't gonna ask my founders to pay for GitHub for this reason - I wouldn't pay for it myself for this reason. This is a very small thing and doesn't require one to pay lots per user just to get this teeny tiny feature.
I knew GitHub had APIs, and I found that GitHub has APIs to manage repository-level secrets too. I planned to just use automation and manage it. The vague idea was - to have a single source of values for the secrets and then use that to put the values in the repository-level secrets using the API. I was thinking of writing some script, or Golang code. And then I thought - well, this is just CRUD, and I need to do this management because I might change these secrets, rotate them etc, or else I could just manually put in all the values if it's just a one-time task. So, CRUD, APIs, and Terraform popped up in my mind.
I looked for Terraform Provider for GitHub and there was one! https://registry.terraform.io/providers/integrations/github/latest
I then looked for the Terraform resource to manage repository-level secrets and found this - github_actions_secret - https://registry.terraform.io/providers/integrations/github/latest/docs/resources/actions_secret
That's all, I was set to write some terraform code to manage a set of common secrets across multiple private repositories
You can find all the code here - https://github.com/karuppiah7890/github-actions-secrets-terraform
Below are the commands I ran. I have also shown how the output of the commands will look like
First, we use docker-compose command to run a docker container which has terraform installed in it. You can also use docker compose command, which is an alternative
docker-compose up -d
# or
docker compose up -d
The output for this will look like -
$ docker compose up -d
[+] Running 2/2
✔ Network github-secrets-terraform_default Created 0.1s
✔ Container terraform-github Started 0.9s
Next we get inside the docker container and start running terraform commands
docker compose exec github sh
Output -
$ docker compose exec github sh
/terraform/github/src #
Inside the docker container, we run the following commands:
cd 01-secrets/
terraform init
terraform plan -out=tfplan
terraform apply tfplan
The output will look like this -
$ cd 01-secrets/
$ terraform init
Initializing the backend...
Successfully configured the backend "local"! Terraform will automatically
use this backend unless the backend configuration changes.
Initializing modules...
- service_repo_secrets in modules/runner-manager-secrets
Initializing provider plugins...
- Finding latest version of integrations/github...
- Installing integrations/github v5.38.0...
- Installed integrations/github v5.38.0 (signed by a HashiCorp partner, key ID 38027F80D7FD5FB2)
Partner and community providers are signed by their developers.
If youd like to know more about provider signing, you can read about it here:
https://www.terraform.io/docs/cli/plugins/signing.html
Terraform has created a lock file .terraform.lock.hcl to record the provider
selections it made above. Include this file in your version control repository
so that Terraform can guarantee to make the same selections by default when
you run "terraform init" in the future.
Terraform has been successfully initialized!
You may now begin working with Terraform. Try running "terraform plan" to see
any changes that are required for your infrastructure. All Terraform commands
should now work.
If you ever set or change modules or backend configuration for Terraform,
rerun this command to reinitialize your working directory. If you forget, other
commands will detect it and remind you to do so if necessary.
$ terraform plan -out=tfplan
Terraform used the selected providers to generate the following execution plan. Resource actions are indicated with
the following symbols:
+ create
Terraform will perform the following actions:
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id will be created
+ resource "github_actions_secret" "runner_manager_aws_access_key_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "core-service"
+ secret_name = "RUNNER_MANAGER_AWS_ACCESS_KEY_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region will be created
+ resource "github_actions_secret" "runner_manager_aws_region" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "core-service"
+ secret_name = "RUNNER_MANAGER_AWS_REGION"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key will be created
+ resource "github_actions_secret" "runner_manager_aws_secret_access_key" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "core-service"
+ secret_name = "RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token will be created
+ resource "github_actions_secret" "runner_manager_gh_personal_access_token" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "core-service"
+ secret_name = "RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_security_group_id will be created
+ resource "github_actions_secret" "runner_manager_security_group_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "core-service"
+ secret_name = "RUNNER_MANAGER_SECURITY_GROUP_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id will be created
+ resource "github_actions_secret" "runner_manager_subnet_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "core-service"
+ secret_name = "RUNNER_MANAGER_SUBNET_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id will be created
+ resource "github_actions_secret" "runner_manager_aws_access_key_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "ingestion"
+ secret_name = "RUNNER_MANAGER_AWS_ACCESS_KEY_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region will be created
+ resource "github_actions_secret" "runner_manager_aws_region" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "ingestion"
+ secret_name = "RUNNER_MANAGER_AWS_REGION"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key will be created
+ resource "github_actions_secret" "runner_manager_aws_secret_access_key" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "ingestion"
+ secret_name = "RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token will be created
+ resource "github_actions_secret" "runner_manager_gh_personal_access_token" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "ingestion"
+ secret_name = "RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id will be created
+ resource "github_actions_secret" "runner_manager_security_group_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "ingestion"
+ secret_name = "RUNNER_MANAGER_SECURITY_GROUP_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_subnet_id will be created
+ resource "github_actions_secret" "runner_manager_subnet_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "ingestion"
+ secret_name = "RUNNER_MANAGER_SUBNET_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id will be created
+ resource "github_actions_secret" "runner_manager_aws_access_key_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "invoice-service"
+ secret_name = "RUNNER_MANAGER_AWS_ACCESS_KEY_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_region will be created
+ resource "github_actions_secret" "runner_manager_aws_region" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "invoice-service"
+ secret_name = "RUNNER_MANAGER_AWS_REGION"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key will be created
+ resource "github_actions_secret" "runner_manager_aws_secret_access_key" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "invoice-service"
+ secret_name = "RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token will be created
+ resource "github_actions_secret" "runner_manager_gh_personal_access_token" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "invoice-service"
+ secret_name = "RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id will be created
+ resource "github_actions_secret" "runner_manager_security_group_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "invoice-service"
+ secret_name = "RUNNER_MANAGER_SECURITY_GROUP_ID"
+ updated_at = (known after apply)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_subnet_id will be created
+ resource "github_actions_secret" "runner_manager_subnet_id" {
+ created_at = (known after apply)
+ id = (known after apply)
+ plaintext_value = (sensitive value)
+ repository = "invoice-service"
+ secret_name = "RUNNER_MANAGER_SUBNET_ID"
+ updated_at = (known after apply)
}
Plan: 18 to add, 0 to change, 0 to destroy.
─────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
Saved the plan to: tfplan
To perform exactly these actions, run the following command to apply:
terraform apply "tfplan"
$ terraform apply tfplan
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region: Creating...
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_region: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_security_group_id: Creating...
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Creating...
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_subnet_id: Creating...
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region: Creating...
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creating...
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_subnet_id: Creation complete after 5s [id=invoice-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_security_group_id: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_region: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region: Still creating... [10s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region: Still creating... [10s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [10s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id: Still creating... [10s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_region: Creation complete after 19s [id=invoice-service:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_security_group_id: Creation complete after 20s [id=core-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region: Still creating... [20s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id: Still creating... [20s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [20s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region: Still creating... [20s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id: Still creating... [20s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [20s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [20s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creation complete after 20s [id=invoice-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Creation complete after 21s [id=core-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Creating...
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region: Creation complete after 21s [id=ingestion:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region: Creation complete after 21s [id=core-service:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Creating...
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id: Creation complete after 21s [id=ingestion:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_subnet_id: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id: Creation complete after 22s [id=core-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creation complete after 22s [id=core-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id: Still creating... [20s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id: Creation complete after 21s [id=invoice-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [10s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_subnet_id: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Creation complete after 17s [id=ingestion:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creation complete after 16s [id=core-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creation complete after 17s [id=invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Creation complete after 16s [id=ingestion:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Creation complete after 17s [id=ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Creation complete after 17s [id=invoice-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_subnet_id: Creation complete after 17s [id=ingestion:RUNNER_MANAGER_SUBNET_ID]
Apply complete! Resources: 18 added, 0 changed, 0 destroyed.
On running terraform plan again, you will see no changes. Interestingly, though GitHub does not show value of existing secret while trying to edit it, seems like it does have some way to tell if the secret has changed or not at the API level
terraform plan -out=tfplan
Output looks like this now -
$ terraform plan -out=tfplan
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=core-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=core-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=ingestion:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=invoice-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=core-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_REGION]
No changes. Your infrastructure matches the configuration.
Terraform has compared your real infrastructure against your configuration and found no differences, so no changes
are needed.
Now if I change some secrets, say some 3 secrets in each of the repositories, it will look like this -
docker compose down
# change secrets in env file
docker compose up -d
docker compose exec github sh
cd 01-secrets/
terraform plan -out=tfplan
Output looks like this -
$ docker compose down
[+] Running 2/2
✔ Container terraform-github Removed 10.1s
✔ Network github-secrets-terraform_default Removed 0.1s
$ docker compose up -d
[+] Running 2/2
✔ Network github-secrets-terraform_default Created 0.0s
✔ Container terraform-github Started 0.2s
$ docker compose exec github sh
/terraform/github/src # cd 01-secrets/
$ terraform plan -out=tfplan
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=core-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=core-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=invoice-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=core-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=ingestion:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
Terraform used the selected providers to generate the following execution plan. Resource actions are indicated with
the following symbols:
-/+ destroy and then create replacement
Terraform will perform the following actions:
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id must be replaced
-/+ resource "github_actions_secret" "runner_manager_aws_access_key_id" {
~ created_at = "2023-08-17 05:11:07 +0000 UTC" -> (known after apply)
~ id = "core-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:10 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key must be replaced
-/+ resource "github_actions_secret" "runner_manager_aws_secret_access_key" {
~ created_at = "2023-08-17 05:11:05 +0000 UTC" -> (known after apply)
~ id = "core-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:28 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token must be replaced
-/+ resource "github_actions_secret" "runner_manager_gh_personal_access_token" {
~ created_at = "2023-08-17 05:11:09 +0000 UTC" -> (known after apply)
~ id = "core-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:17 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id must be replaced
-/+ resource "github_actions_secret" "runner_manager_aws_access_key_id" {
~ created_at = "2023-08-17 03:49:19 +0000 UTC" -> (known after apply)
~ id = "ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:32 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key must be replaced
-/+ resource "github_actions_secret" "runner_manager_aws_secret_access_key" {
~ created_at = "2023-08-17 03:54:38 +0000 UTC" -> (known after apply)
~ id = "ingestion:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:30 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token must be replaced
-/+ resource "github_actions_secret" "runner_manager_gh_personal_access_token" {
~ created_at = "2023-08-17 03:49:14 +0000 UTC" -> (known after apply)
~ id = "ingestion:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:26 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id must be replaced
-/+ resource "github_actions_secret" "runner_manager_aws_access_key_id" {
~ created_at = "2023-08-17 05:50:08 +0000 UTC" -> (known after apply)
~ id = "invoice-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:33 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key must be replaced
-/+ resource "github_actions_secret" "runner_manager_aws_secret_access_key" {
~ created_at = "2023-08-17 05:50:35 +0000 UTC" -> (known after apply)
~ id = "invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:29 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
# module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token must be replaced
-/+ resource "github_actions_secret" "runner_manager_gh_personal_access_token" {
~ created_at = "2023-08-17 05:50:02 +0000 UTC" -> (known after apply)
~ id = "invoice-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN" -> (known after apply)
~ plaintext_value = (sensitive value) # forces replacement
~ updated_at = "2023-09-28 03:39:08 +0000 UTC" -> (known after apply)
# (2 unchanged attributes hidden)
}
Plan: 9 to add, 0 to change, 9 to destroy.
─────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
Saved the plan to: tfplan
To perform exactly these actions, run the following command to apply:
terraform apply "tfplan"
As you can see, it shows a diff / difference. Now we can apply the changes!
terraform apply tfplan
Output looks like this -
$ terraform apply tfplan
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Destroying... [id=ingestion:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Destroying... [id=invoice-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Destroying... [id=core-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Destroying... [id=invoice-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Destroying... [id=core-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Destroying... [id=ingestion:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Destroying... [id=ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Destroying... [id=invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Destroying... [id=core-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Destruction complete after 0s
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Creating...
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Destruction complete after 2s
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Creating...
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Destruction complete after 3s
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Destruction complete after 5s
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creating...
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Destruction complete after 6s
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Destruction complete after 8s
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creating...
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Destruction complete after 9s
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Creating...
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Still destroying... [id=invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY, 10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Still destroying... [id=ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID, 10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Destruction complete after 10s
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Creating...
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Destruction complete after 12s
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creating...
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [10s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Creation complete after 18s [id=ingestion:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Still creating... [10s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [10s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Still creating... [10s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [20s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [20s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Still creating... [20s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [20s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Still creating... [20s elapsed]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Creation complete after 27s [id=ingestion:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [20s elapsed]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creation complete after 26s [id=invoice-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Creation complete after 25s [id=core-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Creation complete after 24s [id=invoice-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creation complete after 22s [id=core-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Still creating... [20s elapsed]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Creation complete after 22s [id=core-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Creation complete after 21s [id=ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Creation complete after 19s [id=invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
Apply complete! Resources: 9 added, 0 changed, 9 destroyed.
If you try terraform plan again, it will show no diff / difference
terraform plan -out=tfplan
Output looks like this -
$ terraform plan -out=tfplan
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=core-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=ingestion:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=core-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_gh_personal_access_token: Refreshing state... [id=invoice-service:RUNNER_MANAGER_GH_PERSONAL_ACCESS_TOKEN]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_security_group_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_SECURITY_GROUP_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_subnet_id: Refreshing state... [id=core-service:RUNNER_MANAGER_SUBNET_ID]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_secret_access_key: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_SECRET_ACCESS_KEY]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_region: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_REGION]
module.service_repo_secrets["ingestion"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=ingestion:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["invoice-service"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=invoice-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
module.service_repo_secrets["core-service"].github_actions_secret.runner_manager_aws_access_key_id: Refreshing state... [id=core-service:RUNNER_MANAGER_AWS_ACCESS_KEY_ID]
No changes. Your infrastructure matches the configuration.
Terraform has compared your real infrastructure against your configuration and found no differences, so no changes
are needed.
So, that's how we manage GitHub Actions Secrets across multiple Private Repositories on GitHub using Terraform to avoid paying for GitHub and still be on GitHub Free Plan




